Day 48: Automating Infrastructure Deployment with AWS CloudFormation
100 Days of Cloud (AWS)
I'm Zin Lin Htet. Who love to learn and share about Linux, Cloud, Docker and K8s. Currently working as a DevOps Engineer at one of the famous Fintech Company in Myanmar.
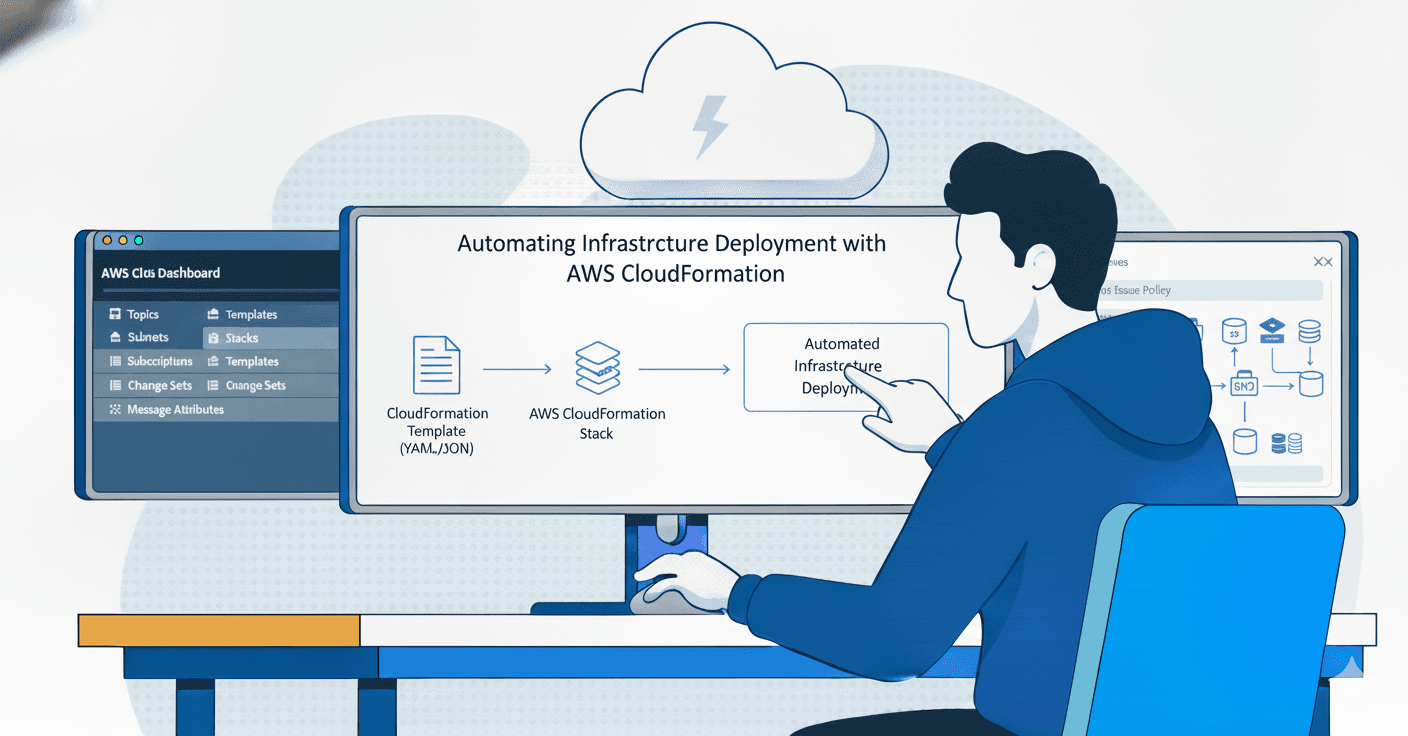
Welcome to Day 48. Today we will learn how to automating Infrastructure depoloyment with AWS CloudFormation.
What is AWS CloudFormation?
AWS CloudFormation is an Infrastructure as Code (IaC) service that allows you to model, provision, and manage your AWS resources by writing a declarative template.
Instead of manually clicking through the AWS Console to create servers, databases, or networking components, you define your entire infrastructure in a JSON or YAML file. CloudFormation then acts as the "architect," reading your plan and building the resources in the correct order.
Core Concepts
Template: A text file (YAML or JSON) that serves as the blueprint for your infrastructure. It defines what resources you want (e.g., an EC2 instance or an S3 bucket) and their configurations.
Stack: When CloudFormation processes a template, it creates a "Stack." This is a single unit of managed resources. If you delete the stack, all resources defined in the template are deleted together.
Change Sets: Before updating a live environment, you can generate a Change Set. This allows you to see a preview of how proposed changes will impact your running resources before you apply them.


AWSTemplateFormatVersion: '2010-09-09'
Description: CloudFormation template to create a Lambda function and IAM role.
Resources:
# IAM Role for Lambda Execution
LambdaExecutionRole:
Type: AWS::IAM::Role
Properties:
RoleName: lambda_execution_role
AssumeRolePolicyDocument:
Version: '2012-10-17'
Statement:
- Effect: Allow
Principal:
Service:
- lambda.amazonaws.com
Action:
- sts:AssumeRole
ManagedPolicyArns:
- arn:aws:iam::aws:policy/service-role/AWSLambdaBasicExecutionRole
# Lambda Function
XfusionLambdaFunction:
Type: AWS::Lambda::Function
Properties:
FunctionName: xfusion-lambda
Handler: index.lambda_handler
Runtime: python3.9
Role: !GetAtt LambdaExecutionRole.Arn
Code:
ZipFile: |
import json
def lambda_handler(event, context):
message = "Welcome to KKE AWS Labs!"
print(message)
return {
'statusCode': 200,
'body': json.dumps(message)
}
Outputs:
LambdaArn:
Description: ARN of the created Lambda function.
Value: !GetAtt XfusionLambdaFunction.Arn
aws cloudformation validate-template --template-body file:///root/xfusion-lambda.yml
aws cloudformation create-stack --stack-name xfusion-lambda-app --template-body file:///root/xfusion-lambda.yml --capabilities CAPABILITY_NAMED_IAM







Congratulations you did it. It looks good. This lab was successfully completed without any errors. See you in day 49. If you have any issues please let me know I will be happy to assist you. Stay tuned and learn together. If you find my article useful, please kindly like and share it.