How to configure GitHub Actions OIDC with AWS ( Simple way )
I'm Zin Lin Htet. Who love to learn and share about Linux, Cloud, Docker and K8s. Currently working as a DevOps Engineer at one of the famous Fintech Company in Myanmar.
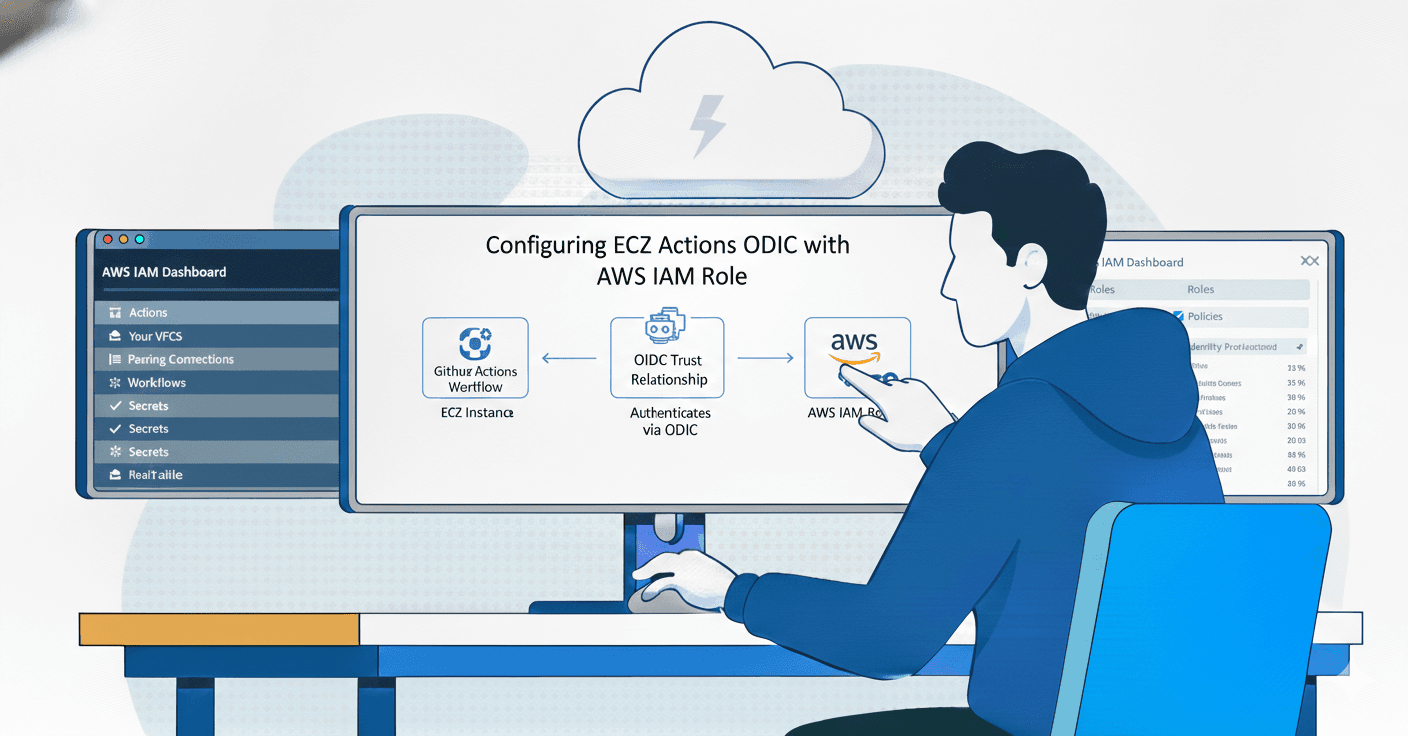
Today I would like to share how to configure GitHub Actions OIDC with AWS. In this lab, you will learn why we use OIDC for AWS. Traditionally, we use an AWS Access Key ID and Secret Access Key as the authentication method to communicate with AWS services.
Imagine you put your AWS key in a GitHub repo, and your GitHub repo gets compromised. Attackers could find and steal your key. Attackers can use your key to create many AWS services, which will increase your cloud bill significantly. If you're using an AWS key in GitHub Actions, you need to regularly rotate the key every month. But, storing or using AWS access and secret keys (long-lived tokens) directly in CI/CD pipelines is considered insecure and not a recommended approach.

If you’re using OIDC instead of an AWS key, you don't need to rotate your OIDC. So what is OIDC? OIDC mean ( OpenID Connect ). OpenID Connect (OIDC) allows your GitHub Actions workflows to access resources in AWS without needing to store AWS credentials as long-lived GitHub secrets. Instead of using password, you just need to setup a Trust Relationship. This means that a GitHub Actions workflow can request a short‑lived OIDC token from GitHub, present it to AWS IAM, and get a temporary role. There is no need to store access keys in secrets.
The main difference is that AWS Access Keys are like a physical key to your house that never expires, while OIDC is like a high-tech "digital badge" that is only valid for a single entry and expires immediately after you leave. In modern CI/CD, OIDC is the industry standard because it eliminates the need to manage, store, or rotate secrets manually.
So let's get started with creating OIDC for our GitHub Actions CI/CD pipeline.

Provider type : OpenID Connect
Provider URL : https://token.actions.githubusercontent.com
Audience : sts.amazonaws.com














name: List VPC
on:
push:
branches:
- main
permissions:
id-token: write
contents: read
jobs:
list_vpc:
runs-on: ubuntu-latest
steps:
- name: Checkout Repository
uses: actions/checkout@v4
- name: AWS Credentials
uses: aws-actions/configure-aws-credentials@v4
with:
role-to-assume: ${{ secrets.AWS_OIDC_ROLE }}
aws-region: ap-southeast-1
- name: List VPC
run: |
aws ec2 describe-vpcs \
--query 'Vpcs[*].{VpcID:VpcId, Name:Tags[?Key==`Name`].Value | [0]}' \
--output table